Enable Your GRC Success Through Powerful, Agile
& Scalable Software.
Risk Under One Roof: Our unique ability to link risk to business objectives in a single platform empowers your organisation to reliably achieve objectives, navigate uncertainty and demonstrate integrity.
You have 42 actions

Trusted by thousands of customers worldwide







One Platform, Complete Trust
What can we help you with?
Redefine the way your organisation views and manages GRC
Effective Governance, Risk and Compliance (GRC) management demands software capabilities to facilitate the sharing of data and insights across your wider risk landscape to drive agility and decision making – that’s where we come in!
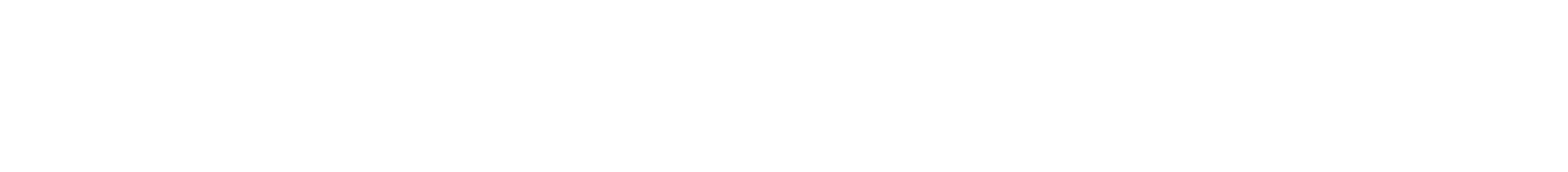
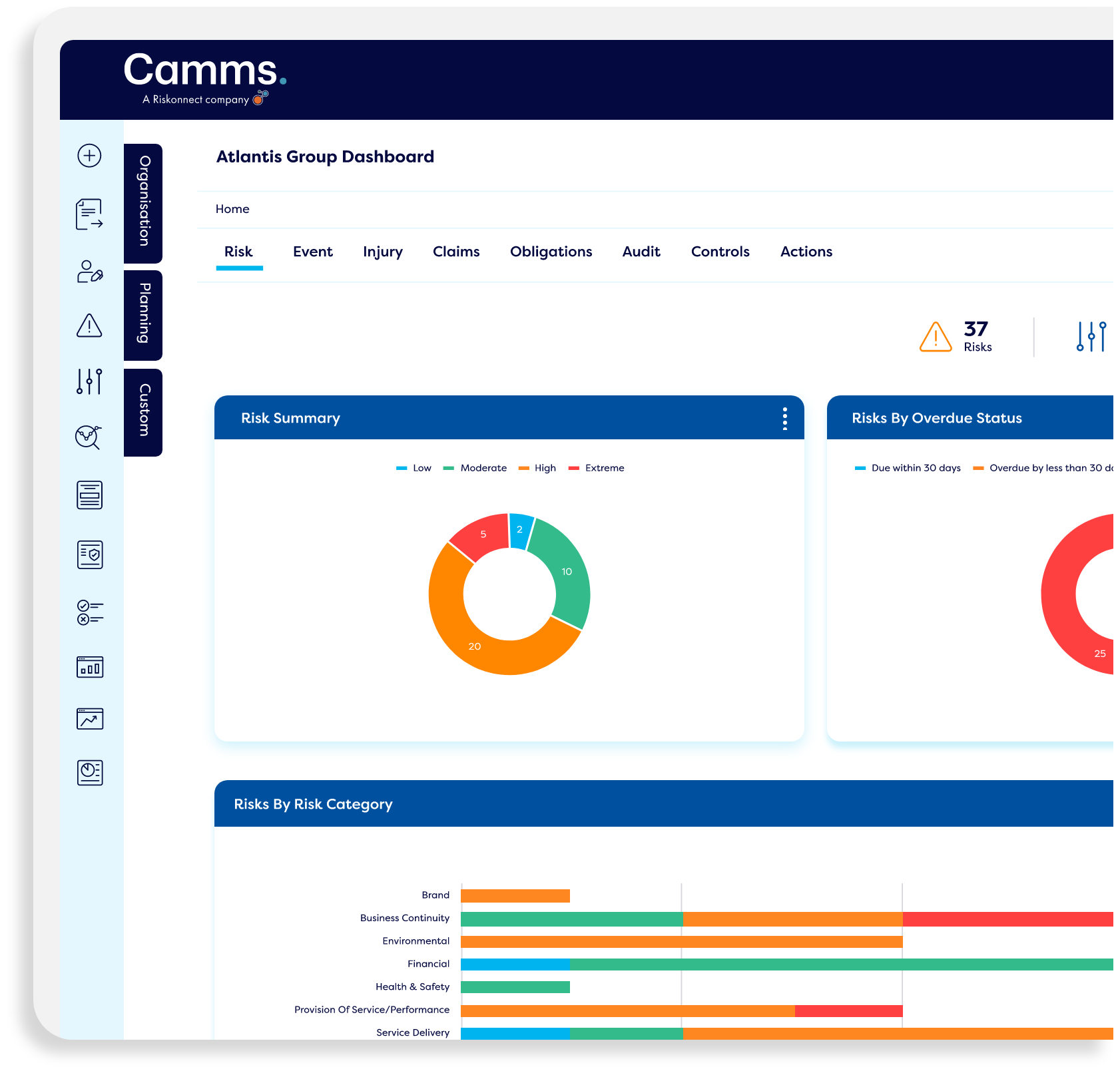
Better and more confident reporting
- Build engaging reports which meet your needs
- Wide range of visualisation and formatting options
- Report to management in a way they can understand
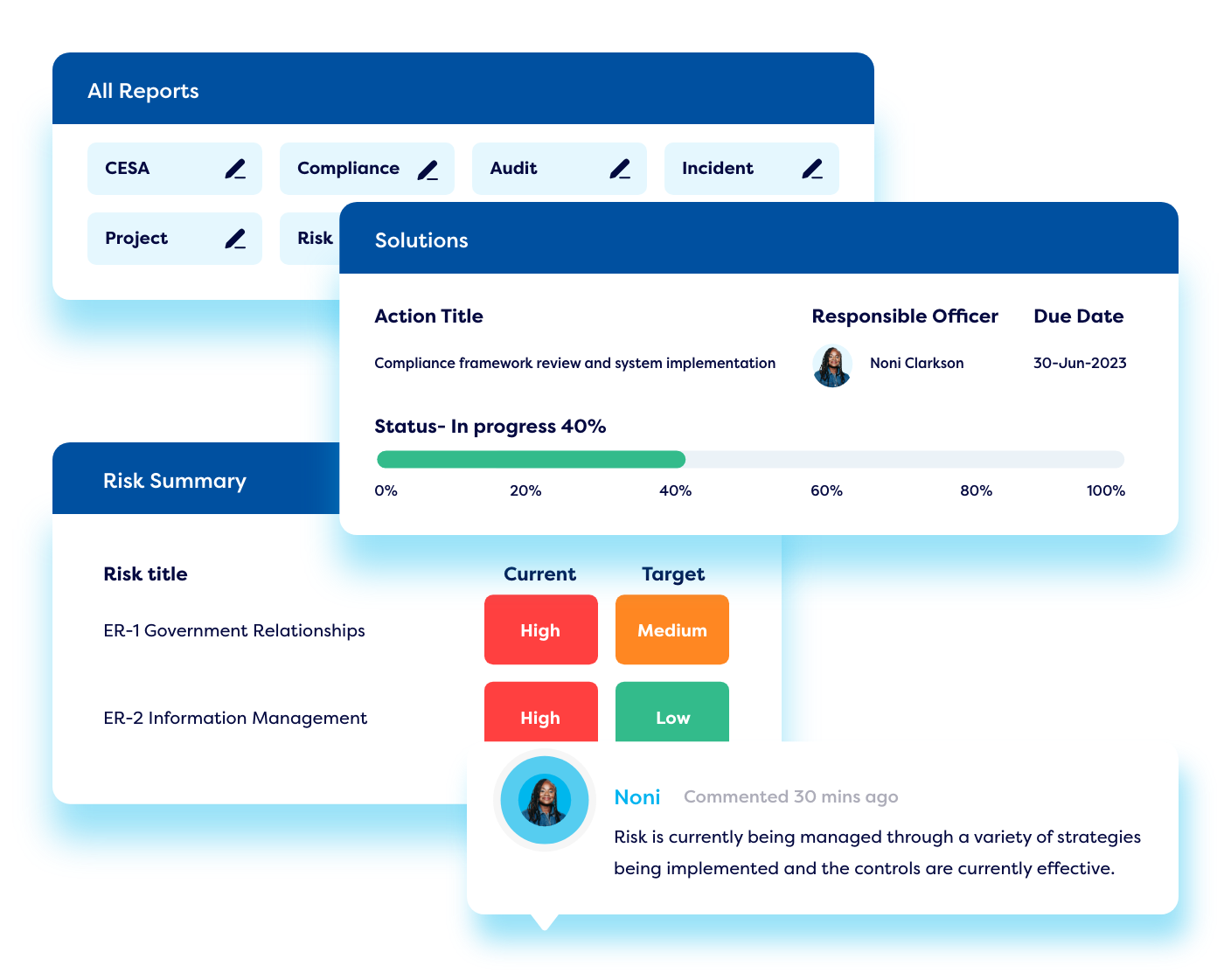
Deliver data to your stakeholders in style
- Interactive dashboards that bring your data to life
- Present information through easy-to-navigate dashboards
- Reach your stakeholders from anywhere, at any time via desktop, mobile or tablet devices
Seamless API integration across your IT ecosystem
- Communicate and exchange data across different software and systems in real-time
- Enable a single source of truth to allow process flow without friction
- Built with security at the forefront, your data is transmitted safely and securely
The Forrester Wave™
Governance, Risk &
Compliance Platforms, Q4
2023

Software solutions that empower teams & drive success
- Governance, Risk & Compliance Software (GRC)
- Business Strategy
- Environmental, Social & Governance (ESG)
- Business Continuity & Resilience
- Portfolio, Programme & Project Management

Governance, Risk & Compliance Software (GRC)
Redefine the way your organisation pursues opportunity and manages risk with our GRC software.
Make the right business decisions with an easy to use solution that provides a comprehensive integrated approach to governance, risk and compliance.

Discover a cloud-based platform that builds on two decades of experience in helping organisations execute effective business strategies.
A comprehensive solution for strategic planning, execution, evaluation and reporting that allows individuals line of sight to see how every single action and task they do drives key organisational goals.

Plan, execute and unlock the value of your ESG strategy and confidently report on the progress of key metrics and initiatives.
Steps to achieving ESG maturity will vary from one organisation to another and at Camms we have the solutions and tools to support you wherever you are on your path to ESG maturity.

Prepare for unexpected disruptions, remain operational in a crisis and recover quickly with our suite of business continuity and operational resilience solutions.
Build a digital process model, conduct Business Impact Assessments (BIAs), monitor threat intelligence, carry out scenario & vulnerability testing to identify gaps and maintain regular plan updates in one platform.
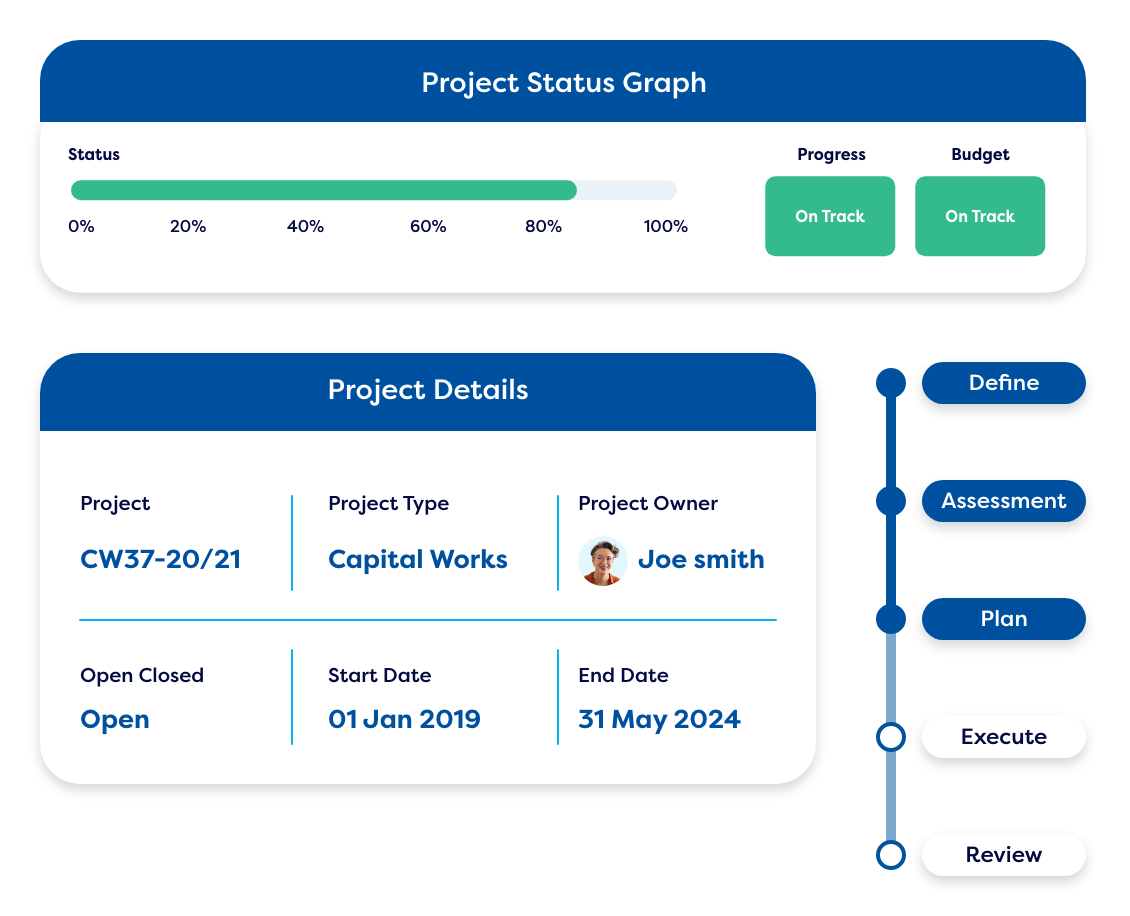
Integrate your risk approach. Allow your business to effectively manage your projects – big or small – in a simple, easy to navigate and understand platform built with the end-user in mind.
Overcome the complexities of modern-day project and portfolio management using a flexible solution that can adapt processes and workflow, integrate with third-party systems and deliver tangible results.
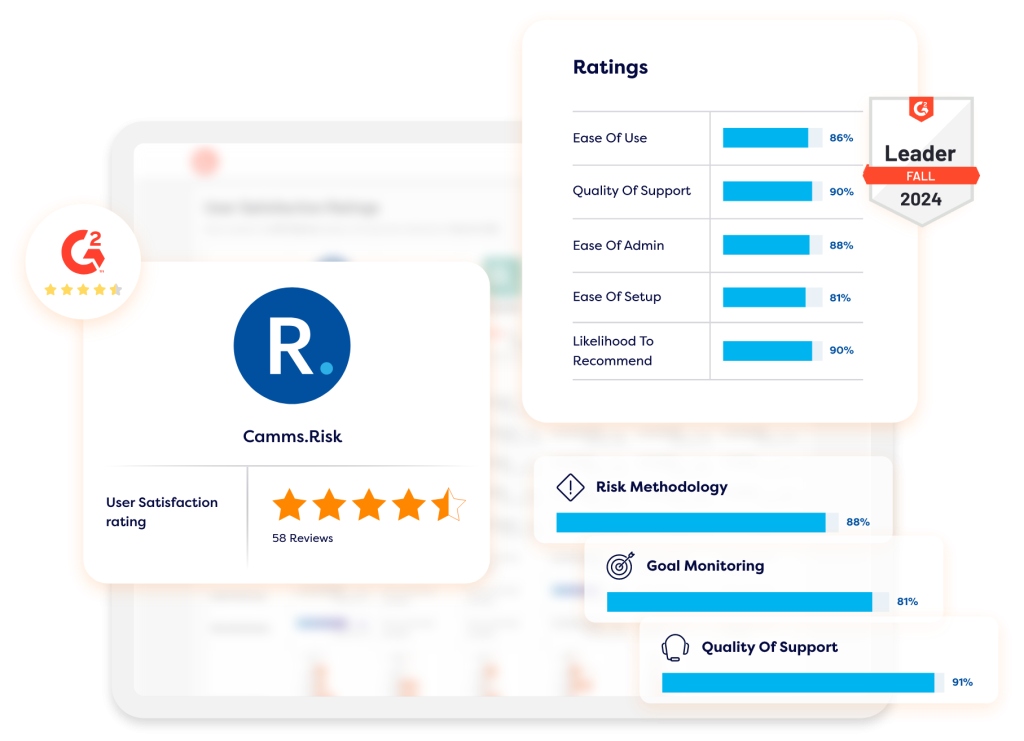
Reviews from happy users
Camms have delivered a fully configurable Enterprise Risk Management solution that’s simple and intuitive for both users and administrators, easily integrates with our existing systems and incident management needs, and supports our risk management framework direction and maturity aspirations.

The Camms Project Delivery and technical team have gone above and beyond during the installation, configuration, and User Acceptance Testing (UAT) phases of the project delivery to ensure the end product functioned correctly and met all of the users’ requirements. The delivered product has modernized the RAF’s reporting processes. It will enable a step-change in risk and performance reporting for the RAF, allowing in-depth reporting on risks and performance targets. The product is highly configurable and has managed to accommodate the complicated RAF structure and reporting processes well.

Camms has provided us an opportunity to reduce the time overhead of manually manipulating data by automating reporting and reminders, and provided a more robust system for managing risk, compliance, audit and incident activities. The simplicity of the system has meant that there is more engagement from the business in managing its compliance and assurance activities, while the automated reporting has reduced the time it takes to complete monthly reports.

From commencement, the Camms Team maintained exceptional service, and their commitment to get to know our organisation and our needs was second to none. We had an incredible and efficient onboarding experience which was supported by the responsive communication style and the knowledgeable advice and guidance. Camms offer an incredible product that supports our ability to evolve our risk culture and strategy. We would recommend Camms to anyone considering a GRC solution for their business.

Camms user-friendly interface is designed to be intuitive and straightforward, allowing our staff to effortlessly navigate the system with minimal training. The Camms team demonstrated exceptional responsiveness and offered invaluable assistance every step of the way, ensuring a smooth and successful implementation process.

Work smarter & faster
Enterprise risk management software comparison reports
Featured content
CPS 230 Readiness Checklist
On the 1st July 2025, compliance with the CPS 230 operational risk management standard became mandatory for APRA regulated financial institutions in Australia.

OAIC Figures Show Data Breaches in Australia Are on the Rise
In May 2025, the Office of the Australian Information Commissioner (OAIC) reported that it was notified of 1,113 data breaches during 2024. These latest figures

Camms to Attend the New Zealand Risk & Resilience Summit 2025
Camms is attending the NZ Risk & Resilience Summit 2025 to showcase how our GRC platform helps organisations manage risk and build resilience through strategy.
Useful resources
Learn all you need to know about complex GRC challenges with our variety of resources.